Pre-launch tenant prep. M&A integration audit. Annual baseline.
One audit, prioritized fix queue, audit-ready evidence. Free 14-day trial.
Three Moments That Demand a Hardening Sprint
These are the inflection points where an unreviewed tenant creates the most risk.
Pre-Launch Readiness
Before going live with a new product, opening a new office, or onboarding a major customer, your tenant needs to be locked down. Default Microsoft configurations leave dozens of gaps that attackers target on day one. A hardening sprint closes them before you're exposed.
M&A Integration Audit
When you acquire a company or merge tenants, you inherit every misconfiguration the acquired organization accumulated over years. A hardening sprint gives you an immediate view of what you've taken on — and what needs remediation before IT integration expands your attack surface further.
Annual Security Baseline
Teams that can't commit to continuous monitoring still need a reliable annual snapshot. A hardening sprint establishes a documented, auditable baseline — benchmarked against CIS M365, NIST 800-53, and your active compliance frameworks — that your team can work from for the next 12 months.
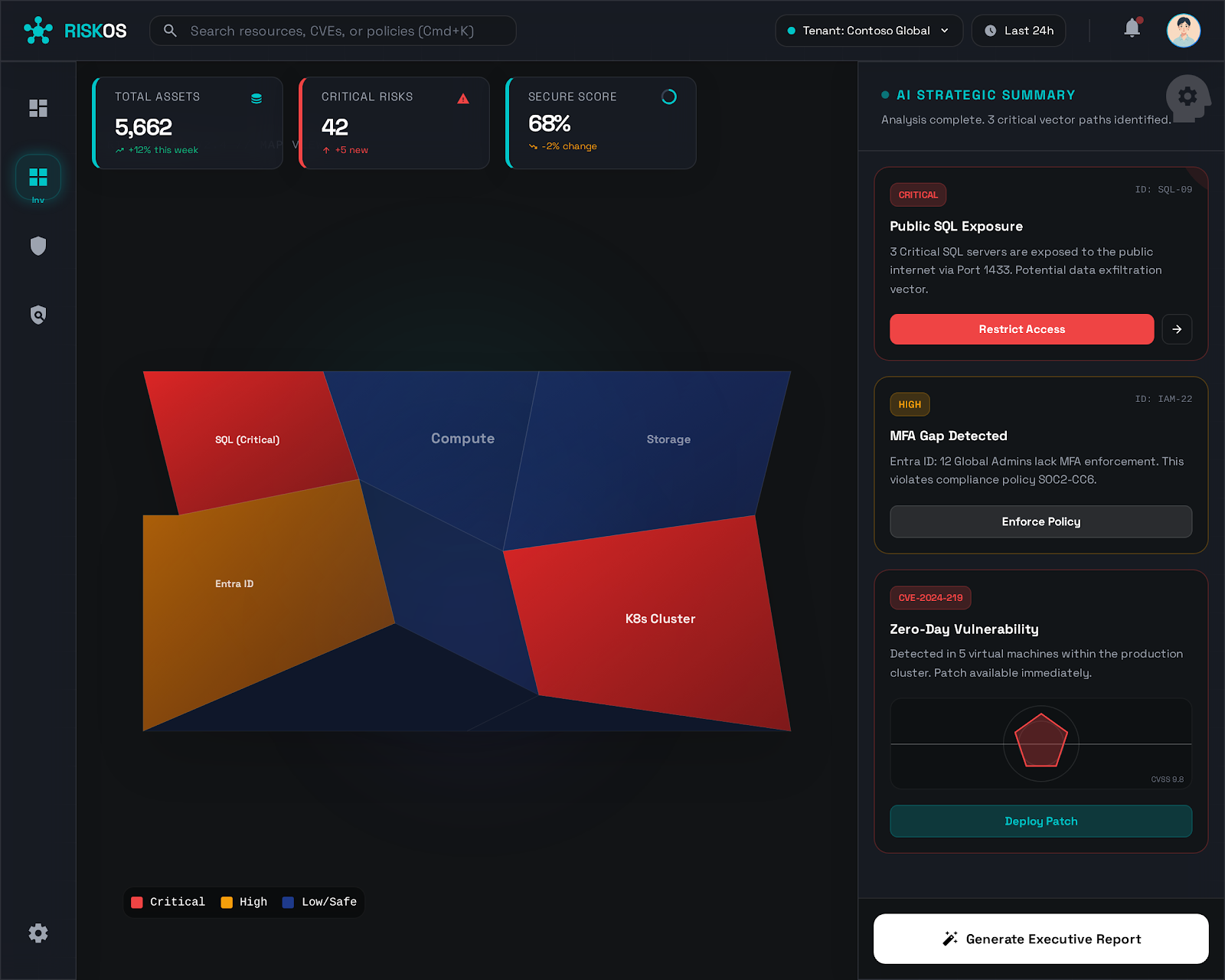
What a Hardening Sprint Actually Delivers
Default Microsoft 365 configurations are not secure configurations. They are designed for broad compatibility, not defense. A new tenant out of the box will have legacy authentication enabled, permissive external sharing, no Conditional Access policies, and dozens of other gaps that experienced attackers probe before anything else.
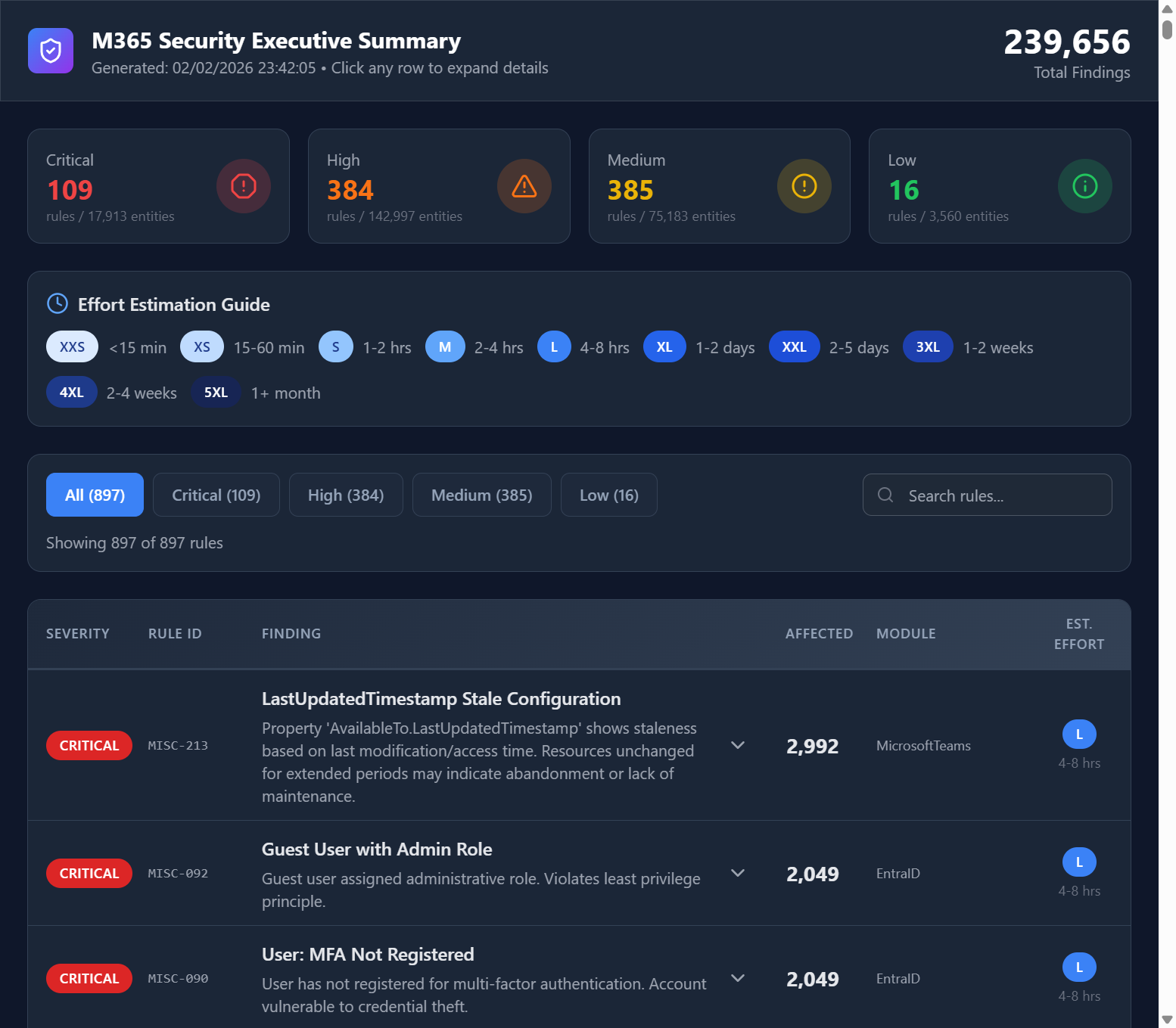
A hardening sprint runs your tenant against 24,000+ curated security rules — covering every layer of Microsoft 365 and Azure — and delivers a ranked, actionable list of every gap that needs closing. Not a generic checklist. Not a consulting deck. A prioritized queue tied to your actual tenant configuration, severity-ranked, and mapped to the CIS M365 Benchmark and your active compliance frameworks.
Your team receives a complete hardening package: the executive summary for leadership sign-off, the technical findings report for your engineers, and a per-control evidence export for your compliance records. The entire assessment completes in under 10 minutes — with zero changes made to your environment.
What's Included
Everything your team needs to identify, prioritize, and close hardening gaps — delivered in a single sprint.
Full-Depth Tenant Assessment
Every M365 workload and Azure resource evaluated — Exchange, SharePoint, Teams, Entra ID, Conditional Access, Intune, Defender, and Azure subscriptions — in a single, unified assessment run.
Prioritized Hardening Queue
Every finding ranked by exploitability, blast radius, and compliance impact. Your engineers know exactly which configurations to close first for maximum risk reduction.
CIS M365 Benchmark Alignment
Every finding mapped to the CIS Microsoft 365 Foundations Benchmark — the industry-standard hardening guide — so your team has both a prioritized fix list and a recognized compliance reference.
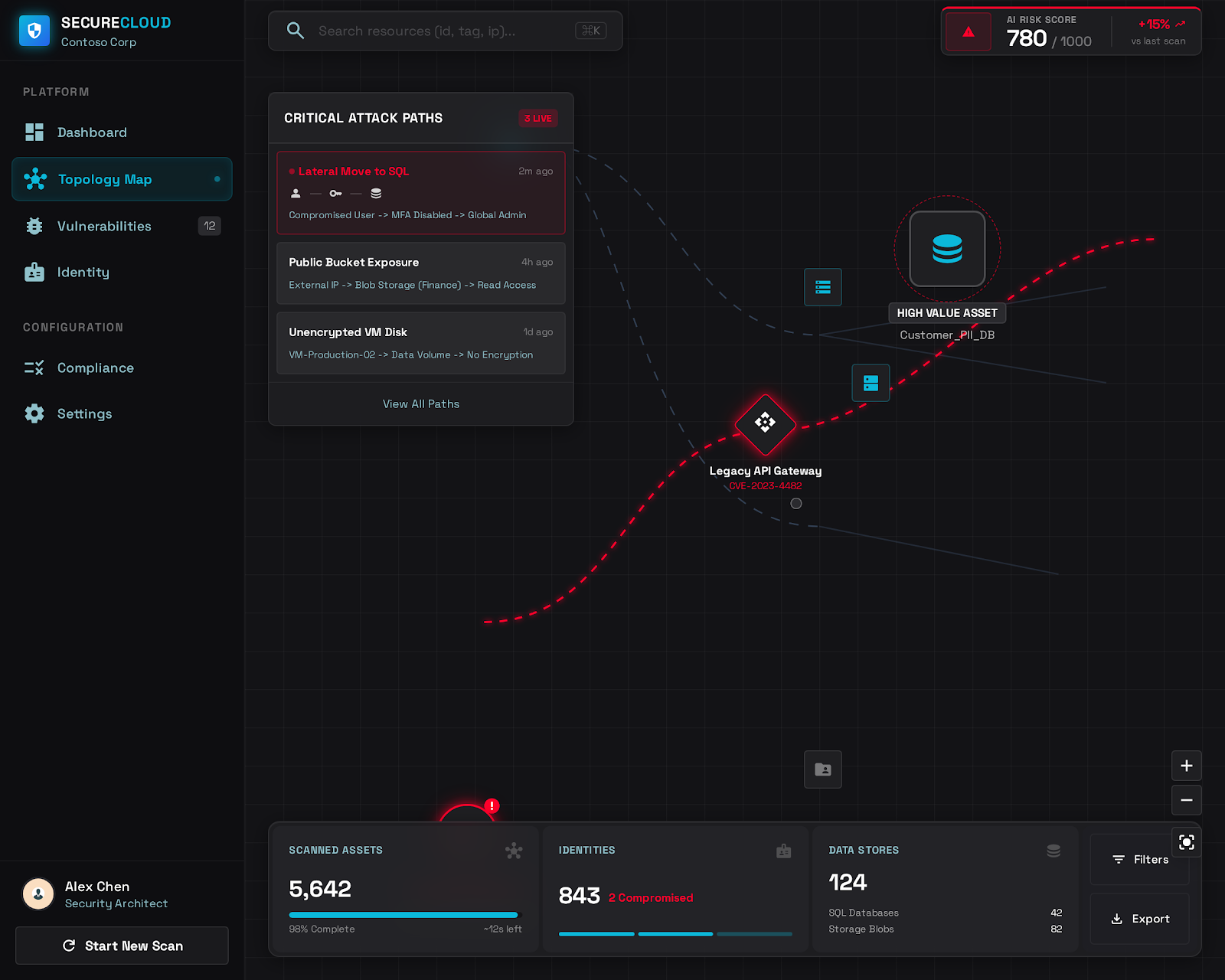
Attack Path Visibility
See how individual misconfigurations chain together into exploitable attack paths — the same way a threat actor would evaluate your environment before a breach attempt.
Executive Summary Report
A non-technical summary of your tenant's current security posture — with overall risk score, top-10 critical findings, and a before/after hardening roadmap — ready for board and leadership review.
M&A Risk Exposure Report
For merger and acquisition scenarios: a structured report of the acquired tenant's security posture that your integration team can use to scope the remediation work before IT systems are connected.
From Assessment to Hardened Tenant
Within 10 minutes — your full exposure is visible
The moment your assessment completes, you have a complete inventory of every misconfiguration across your M365 and Azure environment. Every finding is severity-ranked and mapped to the controls it affects. No waiting. No manual review period.
Within 24 hours — your remediation plan is ready
Your engineers have a step-by-step hardening queue: which settings to change, in which order, and what compliance controls each fix satisfies. Leadership has the executive summary they need to approve the sprint. Work can begin the same day.
Within 30 days — your tenant is hardened and documented
With a focused sprint, your team closes the highest-severity findings and documents every action taken. A second assessment scan confirms the fixes are in place. You now have a documented, auditable hardening record — complete with before-and-after evidence for your compliance records.
What You Walk Away With
Concrete deliverables your team can act on immediately — not a slide deck.
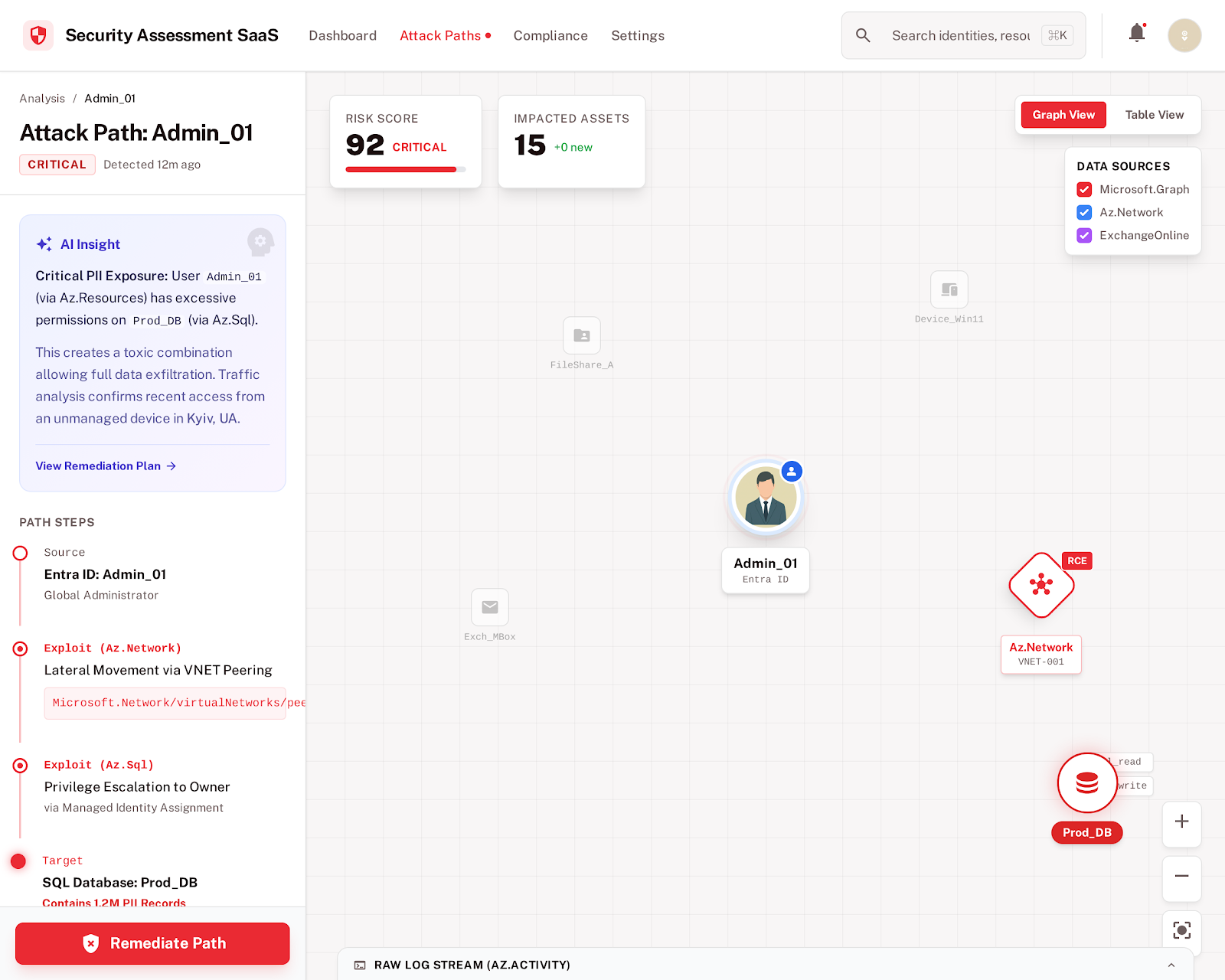
Attack Path Analysis
A visual map of how individual misconfigurations chain into exploitable paths — so your team closes the highest-impact gaps first, not just the highest count.
Prioritized Hardening Queue
Every finding ranked by severity with per-control remediation context. Your engineers pick up the list and work top-to-bottom — no triage required.
Executive Hardening Report
A board-ready summary of your current exposure, your top-10 critical risks, and the projected risk reduction from executing the hardening sprint.
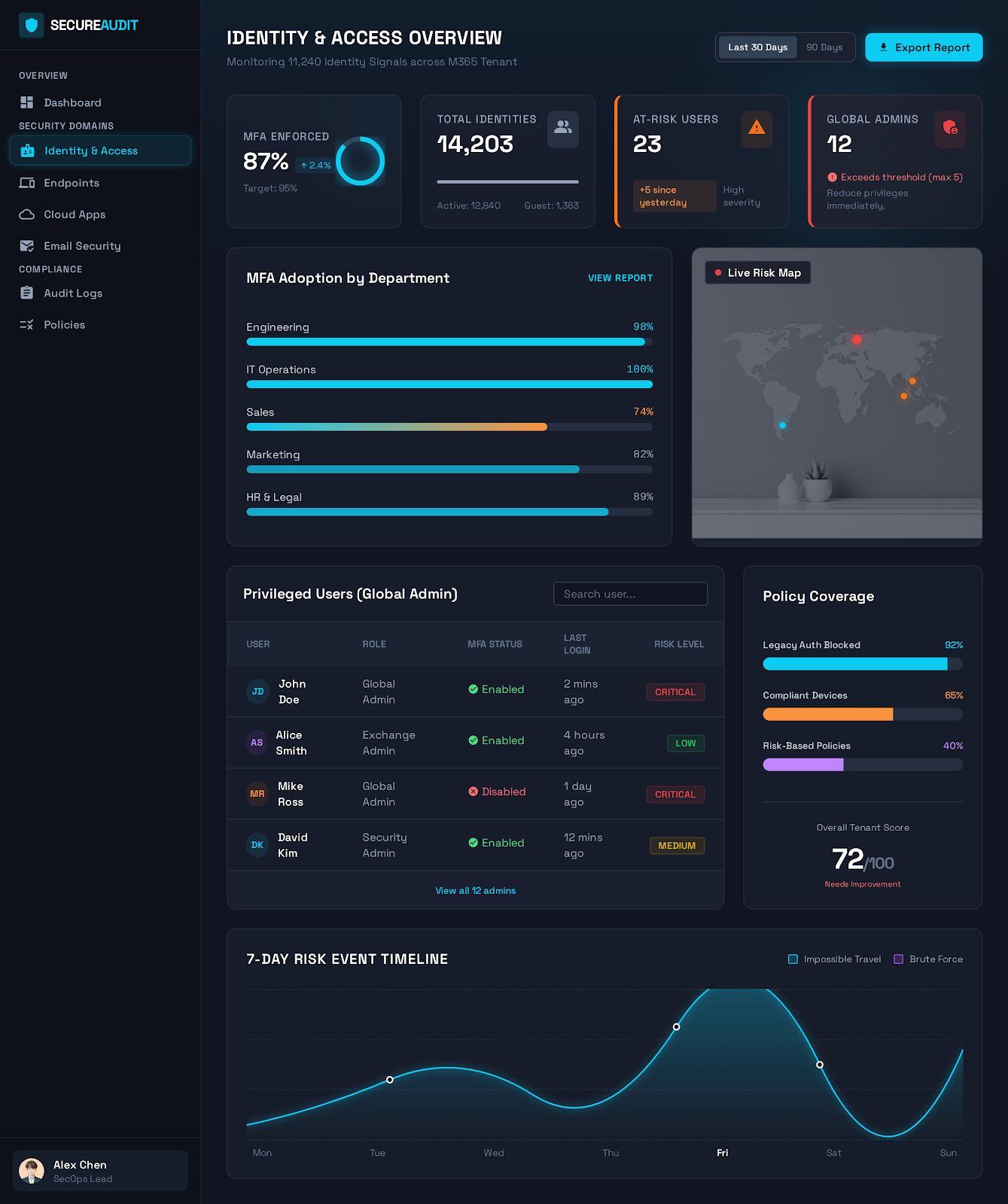
Identity & Access Hardening Report
A deep dive into your Entra ID, Conditional Access, and privileged access posture — the most common initial attack vector in M365 breaches.
Common Questions
Find Every Gap. Close What Matters.
Run your first hardening assessment in minutes. No professional services engagement. No consulting hours. Just findings.
4x Microsoft Solutions Partner — read-only access — results in under 10 minutes.