Pre-breach hardening + post-incident forensic snapshot.
Configuration evidence at point-in-time. MITRE ATT&CK mapped. Free 14-day trial.
Two Phases. One Platform.
Incident readiness is not just about what you do after a breach. It starts with what you close before one happens.
Pre-Breach Readiness
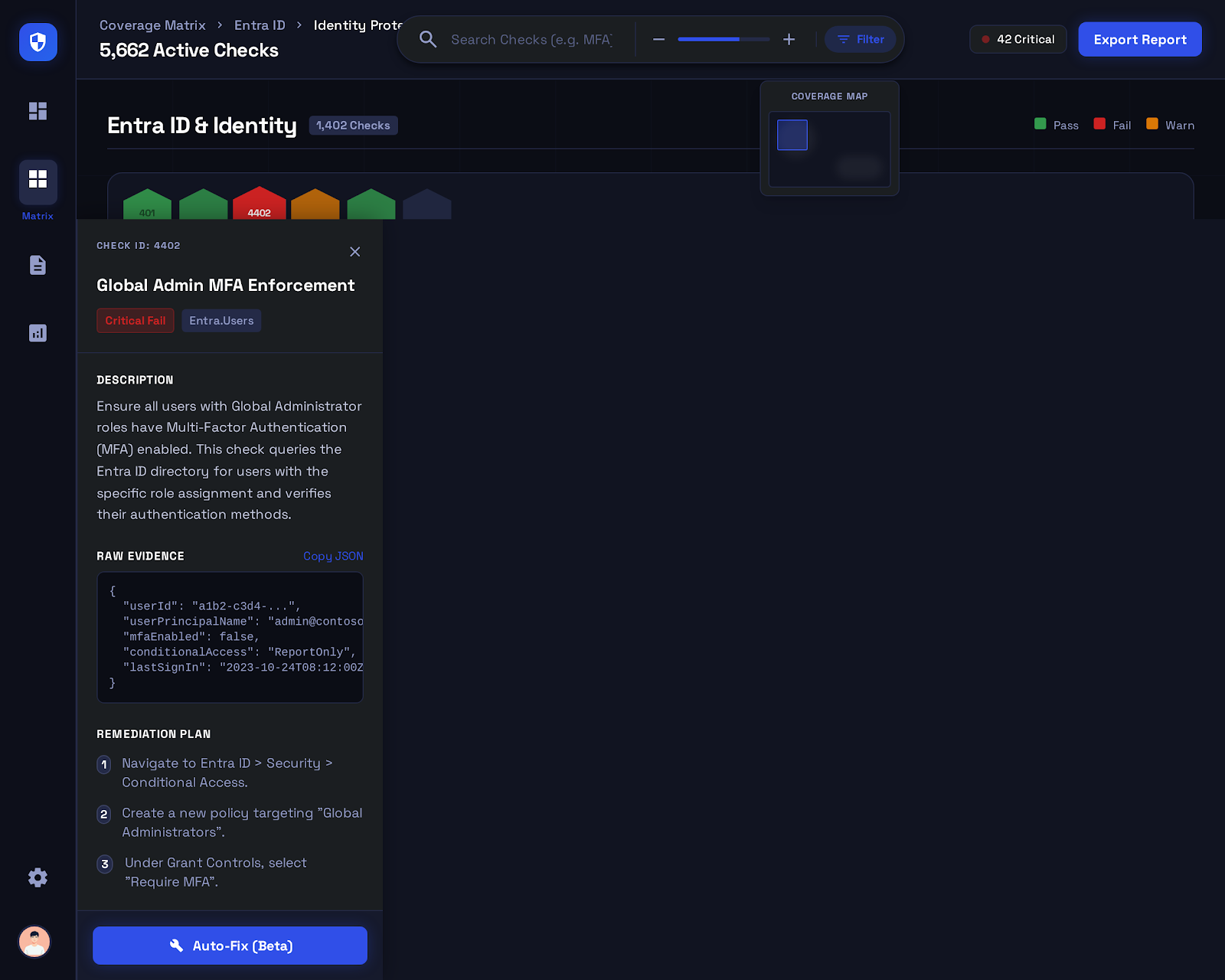
A comprehensive readiness assessment identifies every configuration gap that a threat actor would find and exploit — before they find it themselves. Your team receives a prioritized list of the attack paths available in your current environment, ranked by how quickly an attacker could traverse them.
- Full attack surface inventory across M365 and Azure
- MITRE ATT&CK technique mapping for each critical finding
- Cross-service attack path analysis — how gaps chain together
- Identity and privilege escalation exposure map
- Lateral movement pathway identification
Post-Incident Evidence
When a security incident occurs, the first question your IR team and legal counsel ask is: what did the environment look like at the time of the incident? A post-incident assessment captures a precise record of your M365 and Azure configuration state at a specific point in time — the forensic configuration evidence your investigation depends on.
- Point-in-time configuration snapshot — timestamped and immutable
- Complete record of every security setting across all M365 workloads
- Conditional Access, authentication, and identity state at incident time
- Auditor and legal-counsel ready export of configuration evidence
- Supports regulatory notification and breach disclosure requirements
Why Configuration Evidence Matters More Than You Think
When a security incident occurs in a Microsoft 365 environment, the investigation hinges on understanding what the environment looked like at the time of the breach — not what it looks like today after your team has been remediating for two weeks. Security settings change. Policies get modified. Configurations that existed during the incident window may no longer exist when your incident response team or external forensics firm arrives.
A post-incident assessment captures a complete, timestamped record of every security configuration across your M365 and Azure environment the moment you trigger it — before remediation changes the evidence. Your IR team gets a precise baseline to investigate from. Your legal counsel gets documentation of the control posture at the time of the incident. Regulatory bodies get evidence that supports your breach notification narrative.
For pre-breach readiness, the same depth of coverage serves a different purpose: finding what attackers would find before they find it. Every misconfiguration your assessment surfaces is a path an attacker could have taken — documented, ranked, and mapped to the MITRE ATT&CK technique they would use to exploit it. Close those paths before the incident, and the post-incident investigation becomes shorter, cheaper, and less damaging.
What's Included
Comprehensive coverage for both phases of incident readiness — before and after.
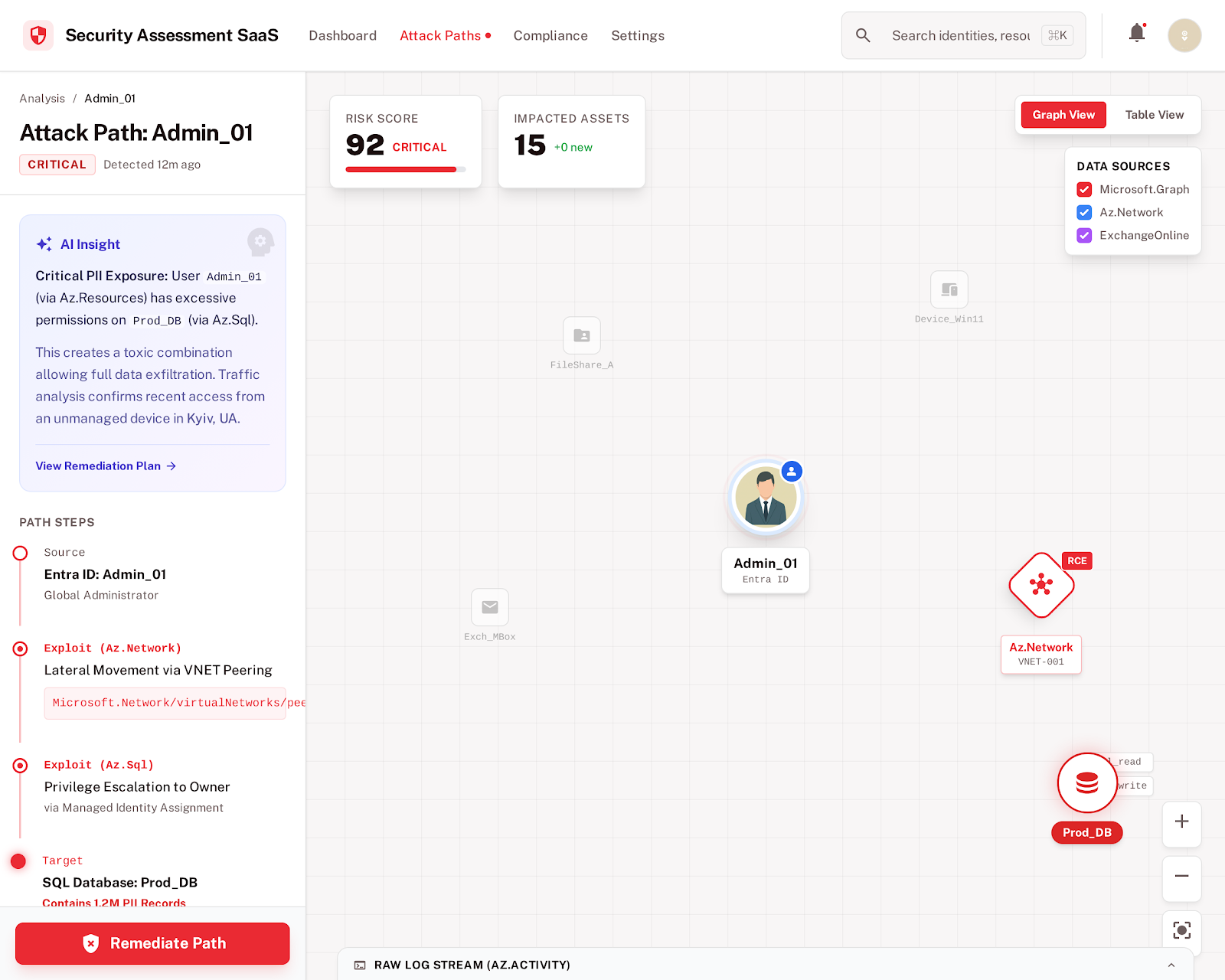
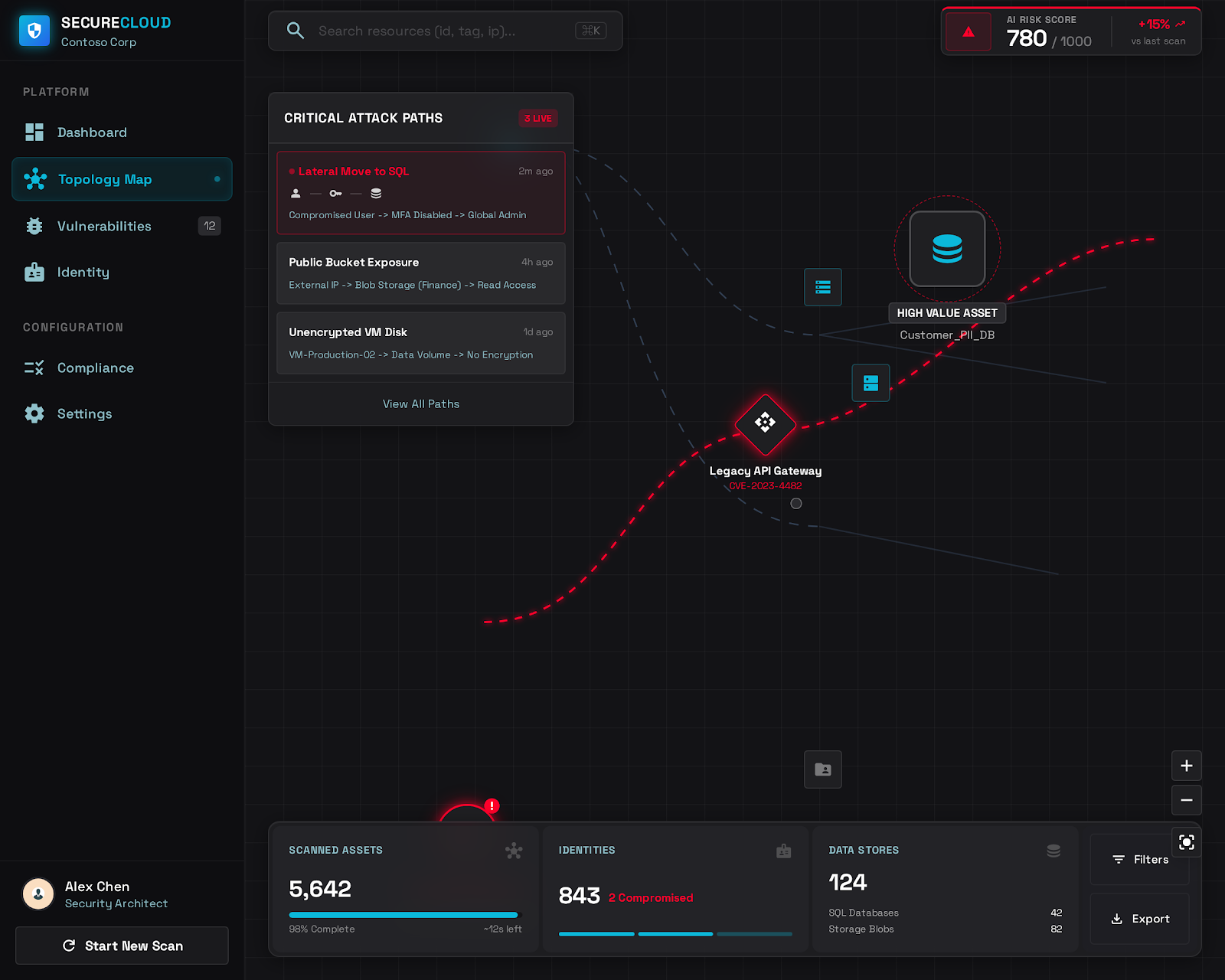
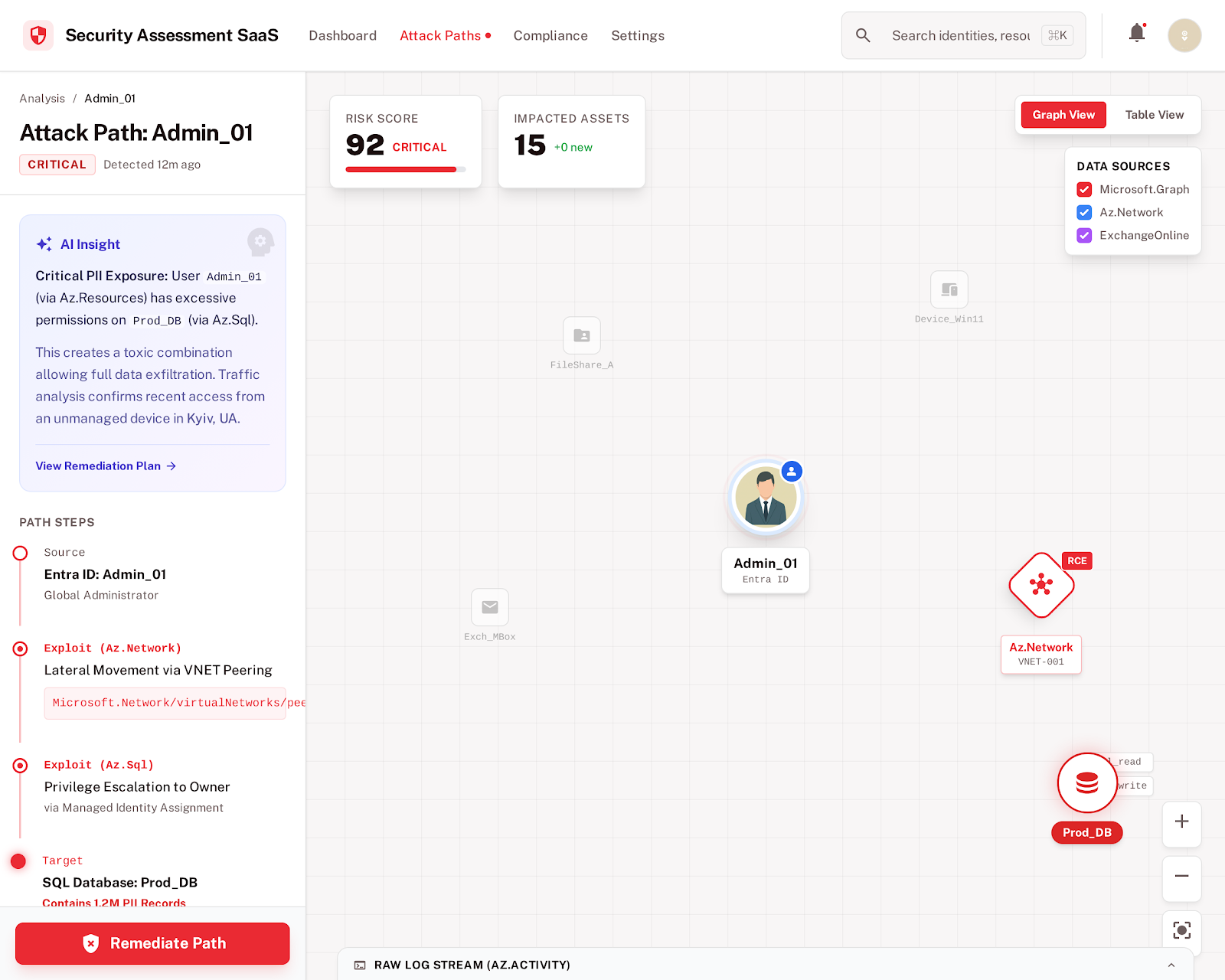
Attack Path Analysis
A visual map of how individual misconfigurations chain into exploitable attack paths across your M365 and Azure environment — from initial access to privilege escalation to data exfiltration.
MITRE ATT&CK Mapping
Every critical finding mapped to the relevant MITRE ATT&CK technique — so your IR team and threat hunters understand exactly which adversary tactics each gap enables.
Point-in-Time Configuration Snapshot
A complete, timestamped record of your environment's security configuration at a specific moment — capturing the state of every M365 workload and Azure resource before remediation begins.
Identity & Privilege Exposure Map
A complete inventory of privileged accounts, admin role assignments, service accounts, and guest access at the time of the snapshot — the starting point for every M365 incident investigation.
Legal & Regulatory Evidence Package
A structured export of the configuration evidence package formatted for use by legal counsel, external forensics firms, cyber insurance carriers, and regulatory notification processes.
Post-Incident Hardening Roadmap
After the investigation concludes, a new assessment identifies every gap that contributed to the incident's impact — ranked for remediation priority so your environment is measurably more resilient before the next threat actor arrives.
Know Which Techniques Apply to Your Environment
MITRE ATT&CK is the threat-informed defense language your SOC, IR team, and threat hunters speak. When critical findings in your assessment are mapped to specific ATT&CK techniques, your defensive priorities become immediately actionable — you know exactly which techniques attackers could execute against your current configuration, and your team can prioritize detections and mitigations accordingly.
- Initial Access techniques enabled by your current configuration
- Privilege Escalation paths through Entra ID and Azure RBAC
- Lateral Movement opportunities across M365 workloads
- Exfiltration vectors through SharePoint, Teams, and Exchange
The Readiness Timeline
What incident readiness looks like in practice — before and after an event.
Within 10 minutes — your attack surface is mapped
A complete readiness assessment returns a prioritized list of every configuration gap, every exploitable attack path, and every MITRE ATT&CK technique your current environment enables. Your security team has an attacker-eye-view of your M365 and Azure posture — without waiting for a penetration test engagement to begin.
Within 30 days — critical attack paths are closed
With a focused remediation sprint, your team closes the highest-severity attack paths and documents every action taken. A verification scan confirms the fixes are in place. Your incident readiness posture is now measurably stronger — and the documentation of that improvement is ready for your cyber insurer, auditors, or board.
Immediately — trigger a forensic configuration snapshot
The moment an incident is declared, trigger a post-incident assessment. Within 10 minutes you have a complete, timestamped record of every security configuration across your M365 and Azure environment at that exact point in time — before your team begins remediation, before configurations change, and before the evidentiary window closes. Your IR team investigates from a reliable baseline. Your legal counsel has documented evidence. Your insurer has the configuration record they need for claims review.
What You Receive
Actionable deliverables for your security team before an incident — and forensic-quality evidence if one occurs.
Pre-Breach Attack Path Report
A complete map of how current misconfigurations chain into exploitable attack paths — with MITRE ATT&CK technique mapping for each path and remediation priority scores.
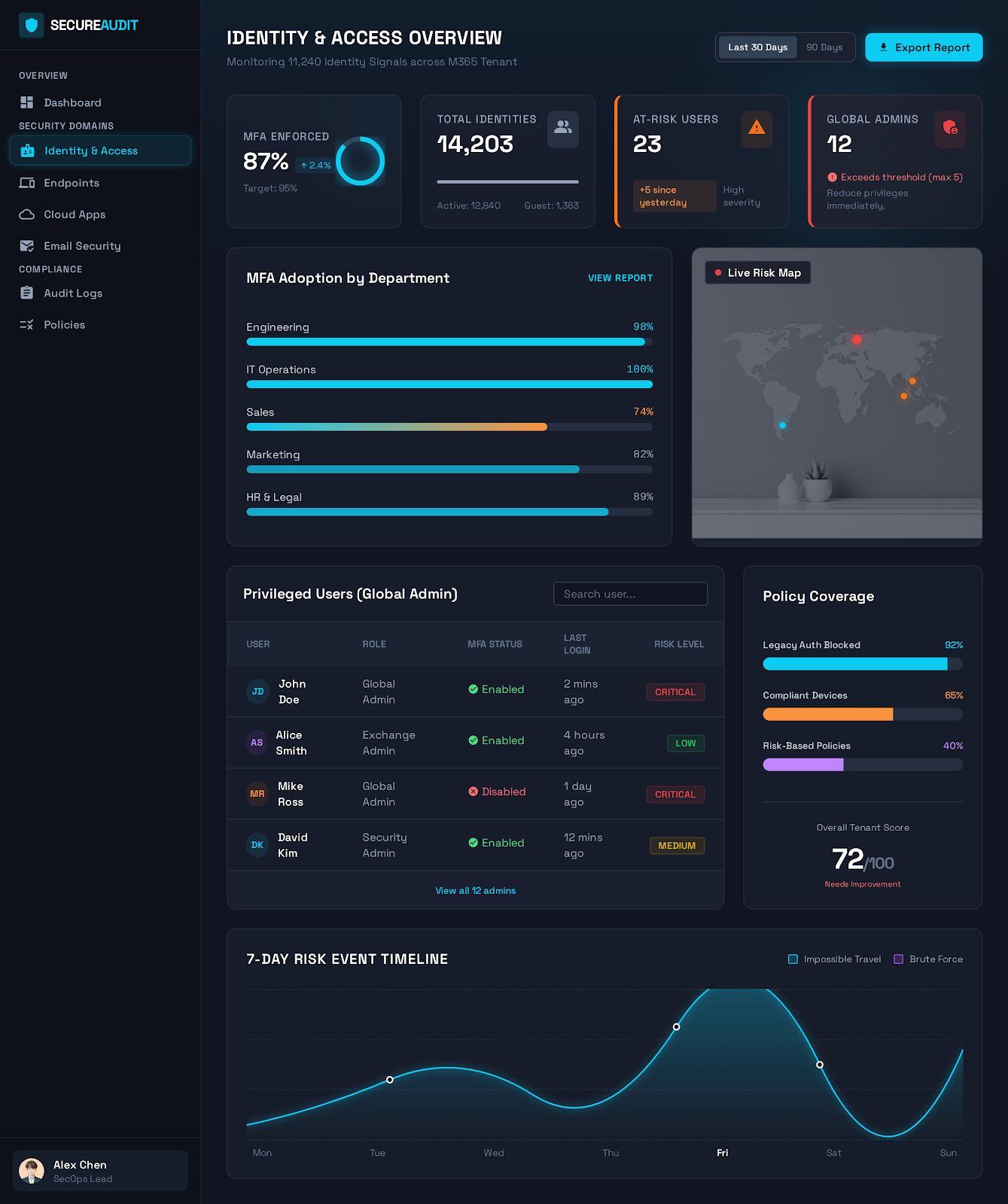
Identity Exposure Snapshot
A timestamped record of all privileged account assignments, admin role holders, Conditional Access policies, and authentication settings — the foundational evidence for any M365 incident investigation.
Forensic Configuration Record
A complete, exportable record of every evaluated configuration point — timestamped at the moment of the post-incident snapshot. Structured for use by IR teams, legal counsel, and cyber insurance adjusters.

Post-Incident Hardening Report
After remediation is complete, a new assessment documents the improved posture — showing leadership, your insurer, and regulators exactly how your organization responded and what controls were strengthened.
Common Questions
Close the Gaps Before They're Exploited. Capture Evidence If They Are.
Start your incident readiness assessment today. Know your attack surface before an attacker does — and have the evidence you need if the worst happens.
4x Microsoft Solutions Partner — read-only access — MITRE ATT&CK mapped findings.